How to: Extract Area Path Permissions from the respective user, and project in Azure DevOps
This script and report extract Area Path Permissions from user. Before that, it’s necessary to get all groups to which that user belongs.
DISCLAIMER: Due to the number of records generated by this report, two mandatory filters were placed: the name of the user and the name of Team Project. This report was based on the ALM Rangers project Extracting effective permissions from TFS
An original script is available on my GitHub repository. See below this script:
Let’s go understand each command used.
- PowerShell script will receive the following parameters:
- $PAT = Personal Access token to connect on Azure DevOps;
- $Organization = Organization URL to list permissions on Area Paths;
- ProjectName = Team Project name that contains Areas to which permissions will be extracted;
- mailAdress = e-mail from respective user to which permissions will be extracted;
- $Connstr = connection string to Azure SQL Database to store the report information. To create this report, it’s necessary to create previously a Azure SQL Server and Database and run a script below:
2. az devops user list = use this command to list all users on Azure DevOps organization. After that, it’s necessary to filter a respective user that was received by parameter.
$allUsers = az devops user list
--org $Organization | ConvertFrom-Json$allUsers = $allUsers.members $allUsers = $allusers.user | where-object {$_.mailAddress -eq $mailAddress}
3. az devops project list = use this command to list all projects on Azure DevOps organization. After that, it’s necessary to filter a respective Team Project that was received by parameter.
$allProjects = az devops project list
--org $Organization --top 500 | ConvertFrom-Json$allProjects = $allProjects.value | Where name -EQ $ProjectName
4. Classification Nodes, Get Root Nodes = use this command to get root Area node under the project.
#Get Root Area Path$AzureDevOpsAuthenicationHeader = @{Authorization = 'Basic ' + [Convert]::ToBase64String([Text.Encoding]::ASCII.GetBytes(":$($PAT)")) }$uriProjectRootArea = $Organization + "/$($ProjectName)/_apis/wit/classificationnodes?api-version=6.0"$ProjectRootAreaResult = Invoke-RestMethod -Uri $uriProjectRootArea -Method get -Headers $AzureDevOpsAuthenicationHeader$ProjectRootAreaResult = $ProjectRootAreaResult.value | Where structureType -EQ "area"$areaRootToken = "vstfs:///Classification/Node/$($ProjectRootAreaResult.identifier)*"
5. az devops security group membership list = use this command to list all groups that user (received by parameter) is contained in.
$activeUserGroups = az devops security group membership list
--id $allUsers.principalName
--org $Organization
--relationship memberof | ConvertFrom-Json6. In Azure DevOps, when working with permissions, it’s necessary to understand SecurityNameSpaces. Basically, each namespace represents the respective set of permissions on Azure DevOps (Git, Area Path, Project Level, Iterations, etc.). In this example, will be used namespace “CSS”, which is represented by the constant below:
$SecurityNameSpaceIdCSS = "83e28ad4-2d72-4ceb-97b0-c7726d5502c3"7. az devops security permission list = use this command to list tokens for given user/group and namespace. In this case, I’ll filter NameSpace CSS and groups to that respective user belongs:
#Get All Tokens from respective group and filter respective project $allAreasTokens = az devops security permission list
--id $SecurityNameSpaceIdCSS
--subject $activeUserGroups.$aug.descriptor | ConvertFrom-Json $allAreasTokens = $allAreasTokens | where-object {$_.token -like $areaRootToken}
8. Token = At the moment that we extract any kind of permission on Azure DevOps, it’s necessary to work with tokens. For each type of permission, there is a specific rule to produce that token. In the specific case of Area Path (CSS) permissions, the rule below is valid:
$areaToken = "vstfs:///Classification/Node/$($ProjectRootAreaResult.identifier)- Identifier = Identifier of respective Area Path.
9. More details about other tokens, can be found in the links below:
- Security tokens for Permissions management;
- Security namespace and permission reference for Azure DevOps
10. az devops security permission show = Show details of permissions available in each namespace
$AreaCommands = az devops security permission show
--id $SecurityNameSpaceIdCSS
--subject $activeUserGroups.$aug.descriptor
--token $aat.token
--org $Organization | ConvertFrom-Json11. After extract all permissions, this information is stored in a table in Azure SQL.
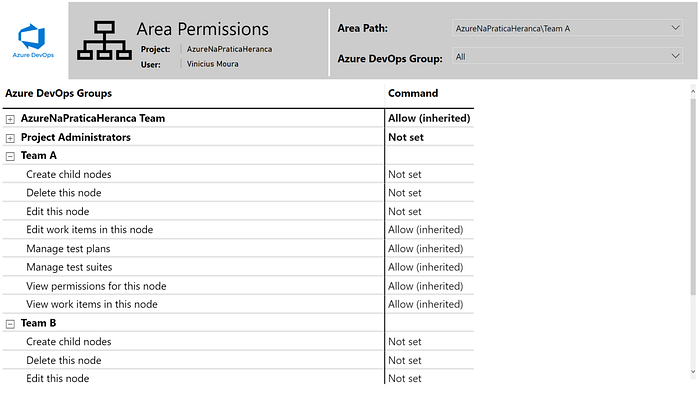
12. After insert information into a table, I connected this database on Power BI:
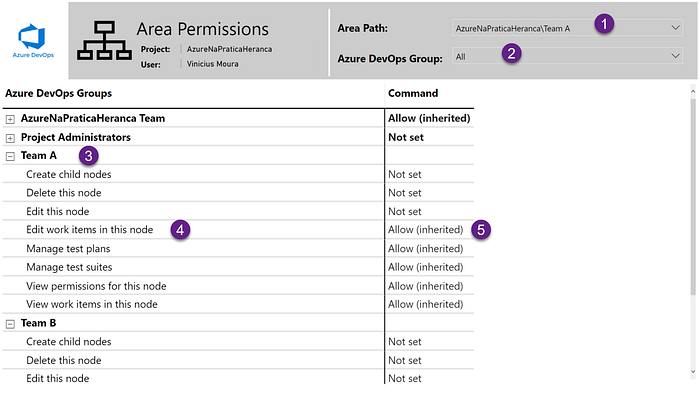
- Area Path (1) = Filter Area Path to verify respective permissions;
- Azure DevOps Groups (2) = Filter Azure DevOps Groups to which the user belongs;
- Azure DevOps Groups (3) = list all Azure DevOps groups to which the user belongs;
- Command (4) = List of commands available to Area Path;
- Permission (5) = Permission type (Allow, Deny, Not set, etc.).
